Data Obfuscation vs. Data Minimization: A School’s Guide to Secure Data Sharing
When it comes to sharing student information with app vendors, schools have two options. The first is data obfuscation, where you transform the data sent to application partners in a way it cannot be reversed. The second is data minimization, where you carefully audit the data sent to application partners, ensuring that unnecessary data isn’t shared.
Both approaches are inherently well-meaning; schools should be very careful about sharing student information. That’s because attackers can get around school organizations’ cybersecurity protections by attacking their application partners instead. Anything that the organization shares with the vendor becomes fair game for the attacker in what’s known as a supply chain attack.
In addition, both the data obfuscation approach and the data minimization approach have their merits. But in our opinion, the drawbacks of data obfuscation outweigh the merits. In the end, data minimization achieves the benefit of security while being a better choice for the realities of the classroom.
What is Data Obfuscation?
Data obfuscation is a security technique that involves permanently transforming the data sent to recipients. A one-way algorithm known as a cryptographic hash will turn a name like Jessie Jones into a random character string like A9i41 NE28U that cannot be reversed back to Jessie Jones. This means that attackers can’t access this data even if they successfully breach the vendor.
Why Would School Districts Employ Data Obfuscation?
Some edtech applications require student data in order to function. But administrators are rightly wary of sharing this information. Since there’s no requirement for the shared data to be accurate, however, the data obfuscation technique effectively tricks the app into using the substituted hash.
What Are the Benefits of Data Obfuscation for Edtech Security?
To recap, there are three main benefits to data obfuscation.
1. Data sent to application partners is permanently encrypted.
2. Even if an attacker successfully completes a supply chain attack, your data is safe.
3. Data obfuscation is theoretically more compliant because PII can’t be exposed during a breach tricks the app into using the substituted hash.
What Are the Drawbacks of Data Obfuscation?
Data Obfuscation Breaks Edtech Applications
Let’s say that you use data obfuscation and successfully present student Jessie Jones as student A9i41 NE28U, with the email address A9i41.NE28U@schoolname.com. A lot of the application’s functionality is now useless.
- The application can’t share important updates, such as grades or homework assignments, using student email addresses.
- Teachers will find it much more difficult to look up student information within individual applications (because now they have to remember that “Jessie” is actually A9i41).
- If the obfuscation method uses a different hash for each application, then it will be nearly impossible to track student performance across different apps.
What’s more, application vendors have found that data obfuscation can actually disrupt the student learning experience. Consider you are logging into your favorite math application and see “Hi, A9i41” on your screen. The student may feel confused – are they in the right account? Are their assignments correct? Just one simple name change could disrupt the entire lesson. In addition, edtech vendors now find that they’re using valuable bandwidth and storage to process meaningless data.
This leads us to our primary thesis as to why data obfuscation isn’t suitable for the edtech environment. If the data you’re sharing is so important that it cannot be seen in its intended form, why are you sharing it in the first place?
What is Data Minimization?
Data minimization is the process of applying the principle of least privilege to data sharing with application vendors. For example, if an application requires a student’s name and email for functionality, you might share those. However, depending on the application, you might choose not to share other information, such as their gender, birthdate, racial backgrounds, and so on.
Drawbacks of Data Minimization
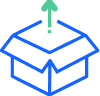
First, it is possible to send data to app vendors that you didn’t intend to share. That being said, Clever’s data minimization controls are set up field by field, and application by application. Having fine control over the data you’re sharing makes these mistakes less likely (though some fields are always necessary – learn more in our help center: For Clever Admins: Apps – Field access).
Second, vendors may need to process some forms of PII in order to provide the full value of their application. This might give some administrators pause, but Clever (along with many other services in the educational technology space) is designed to meet our responsibilities under relevant privacy laws such as COPPA and FERPA to protect personal information contained in students’ educational records. (You can learn more in Clever’s Privacy Policy.)
This brings us to the third drawback – the time and effort required to vet applications and their ability to handle PII. While this might seem like a drawback at first, proper diligence and vetting is foundational to data privacy, governance, and security practices. There are many resources available to support you with data governance and security – including our Cybersecurity Blueprint – complete with standards from industry experts, like NIST and CoSN.
With Clever, Data Minimization Wins Out in the Battle for Information Security
Student Data privacy is the first thing we think about, so you can help students learn in the classroom without worry.
We maintain the highest security standards, while adapting to the classroom environment – so that schools and applications support student learning.
Clever gives school IT leaders control over information access through data minimization. You can enable or disable individual form fields for individual applications, giving you superb control and understanding over your critical data and its ultimate destinations.
While data obfuscation can lock students out of learning, data minimization puts you in control. This lets you balance personalization with student data privacy. Speak with a Clever expert and learn how our security philosophy is tailored for the classroom experience.
Contact a Cybersecurity Specialist

More to read

April 15, 2026
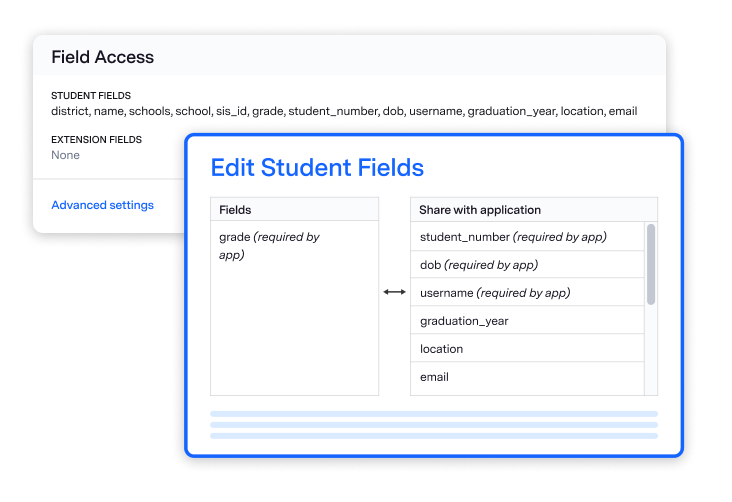
(Student) identities are the new front door for attackers. Is your school ready?The old model of school cybersecurity was built around networks — protect the edge, control the hardware, keep the bad stuff out. That model is gone. Today, your users are the front door. And in K-12, that means millions of student accounts — most of them guarded with just one simple password. That's the reality we dug into during a recent Cybersecure Live webinar. Here’s the breakdown of why the "handle is jiggling" and how to bolt the door.
December 23, 2025
End password chaos: The 5-step guide to secure, age-appropriate logins in schoolsSchool IT departments — take these 5 steps to offload the burden of manual password resets while improving cybersecurity for classrooms.
December 10, 2025
Wonde vs. Clever: 2025 Side-by-Side ComparisonWhen it comes to choosing the right edtech platform for your school or trust, there’s a lot to consider. Can it sync reliably with your Management Information System (MIS)? Support secure logins for every user, on every device? Scale across multiple schools without overloading your IT team? Wonde and Clever are two of the most […]