(Student) identities are the new front door for attackers. Is your school ready?
The old model of school cybersecurity was built around networks — protect the edge, control the hardware, keep the bad stuff out. That model is gone. Today, your users are the front door. And in K-12, that means millions of student accounts — most of them guarded with just one simple password.
That’s the reality we dug into during a recent Cybersecure Live webinar. Here’s the breakdown of why the “handle is jiggling” and how to bolt the door.
The Handle is Always Jiggling: From “Likely” to “Probable”
Emily Dillard, CIO of Alexandria City Public Schools, described her district’s cybersecurity experience with an analogy that stuck: it’s like someone perpetually jiggling your door handle. The door might be locked — but there’s always someone trying to get in.
Dr. Dillard’s team is working to protect the identities of over 16,000 students. They have the systems and staff to keep that door locked. Most districts don’t.
And the stakes are real. A compromised student identity can sell on the dark web for around $300. That’s someone who may not even discover their identity has been stolen by the time they can vote. This worst-case-scenario is what keeps many IT teams up at night.
Widening the Entryway: Vendor Risks and AI Lockpicks
If student accounts are the front door, vendors and AI are the new ways attackers are picking the lock.
According to our recent survey of IT leaders around the world (Cybersecure 2026 Report), more than half of school organizations reported experiencing a cyber incident in the last year. That’s up from 36% in 2024. Of all incidents, those attributed to vendor-related breaches jumped from 4% to 32% in the same period, reflecting how much risk now lives in the connected platforms schools depend on. And 81% of school IT leaders believe AI is actively heightening their security risk — because it is. Bad actors are using AI to execute phishing and account takeover attempts at a scale we’ve never seen before.
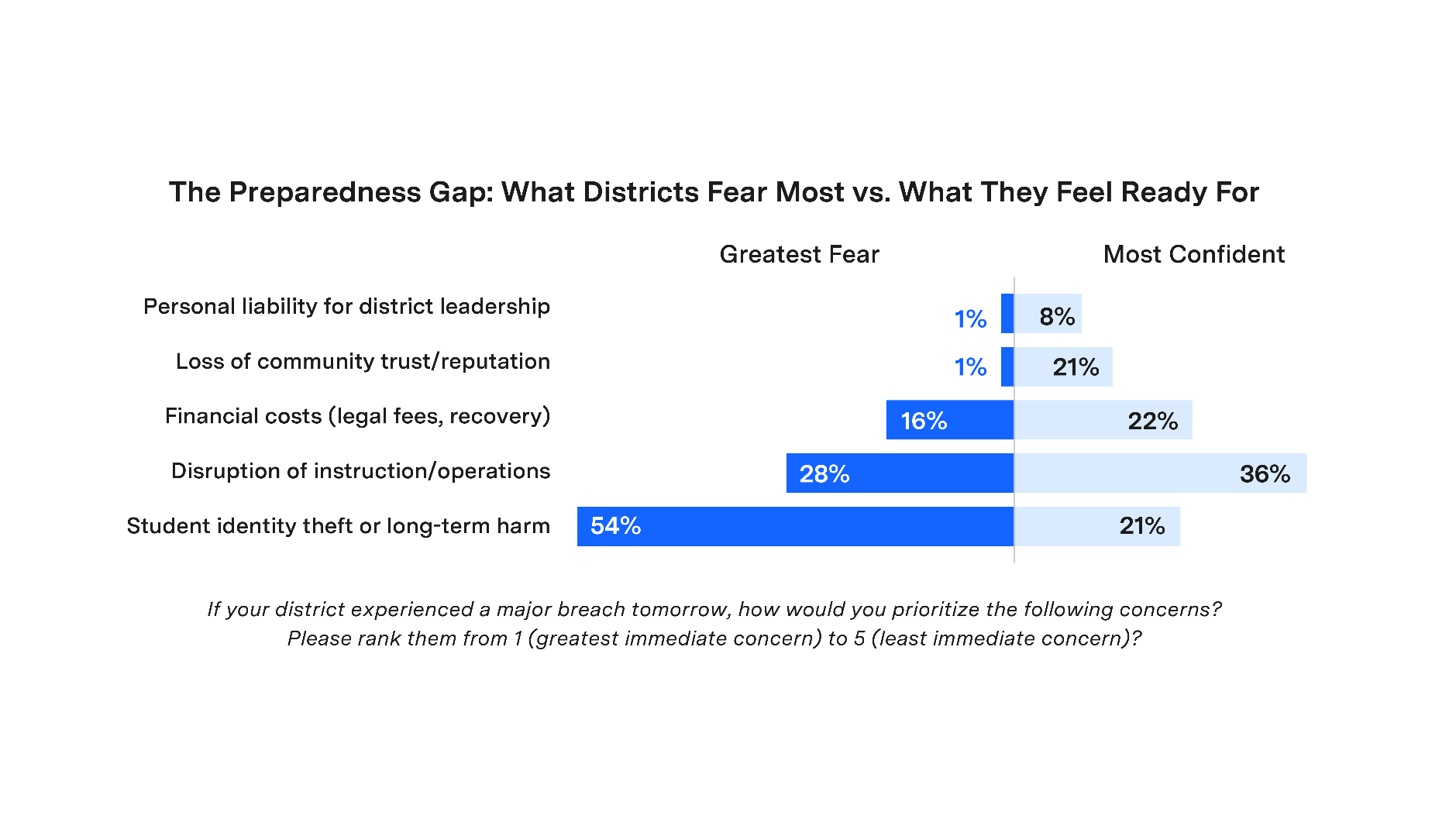
Our survey also found that 54% of school IT admins named identity theft and long-term student harm as their most feared breach outcome. Only 21% felt confident they could handle one.
The Student Access Gap: A Door Without a Bolt
Some good news: Staff MFA adoption is strong — over 90% of districts have it in place for teachers and staff. But student MFA? 13% across all grade levels. That number has barely moved since last year, despite threats accelerating.
This isn’t an awareness problem. IT leaders know student accounts are a vector. The obstacle is implementation — specifically, the reality that standard enterprise MFA tools don’t work in a classroom. You can’t require a phone-based second factor when phones are banned. You can’t deploy hardware tokens at scale to elementary students.
What “Classroom-First” Security Actually Looks Like
The right answer isn’t to skip student MFA because it’s hard. We can’t ask a second-grader to use a hardware token or a banned smartphone for MFA. To secure the “front door,” we need locks that actually fit school life.
What “Classroom-First” security looks like in practice:
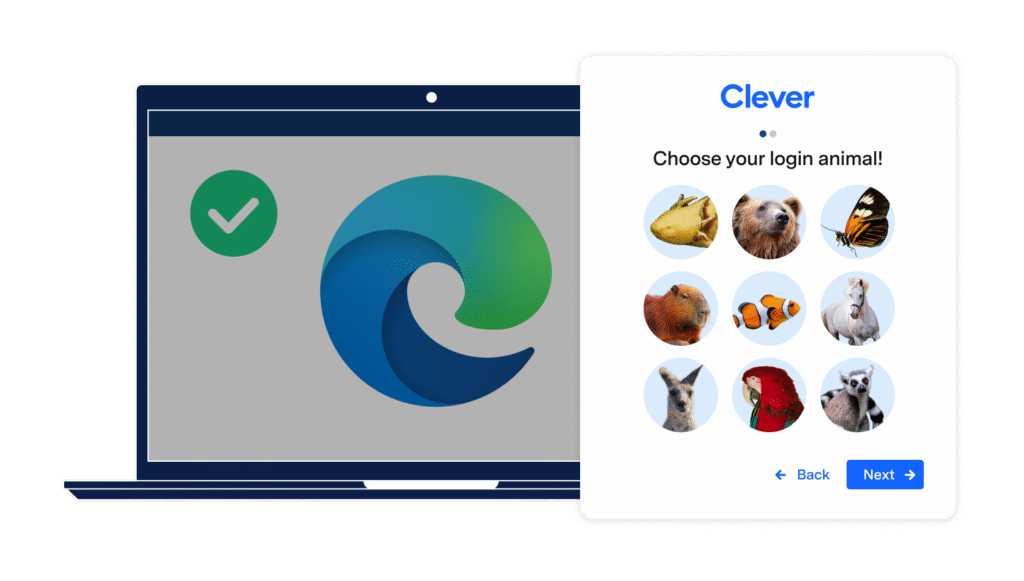
Device-free second factors. PINs and login pictures work for every grade or year level, don’t require a phone, and don’t create a separate device management burden. Todd Pugliese, Director of IT at Mapleton Public Schools, walked through the student experience: power on Chromebook, enter password, select a picture — and they’re in.
Automated account lifecycle management. Every lingering account from a departed student or staff member is an open door. Automated provisioning and deprovisioning closes those doors automatically — no script maintenance required.
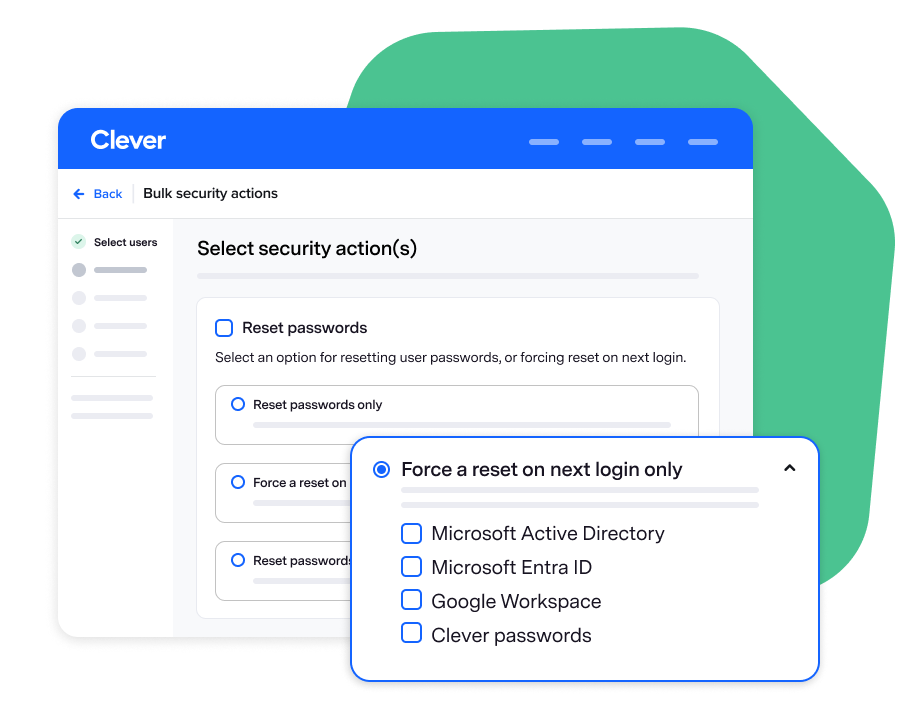
Delegated password management. Teachers and tech leads can reset passwords right in the Clever Portal. That’s hours of helpdesk tickets that never get created.
Integration with what you already have. Whether your school organization runs on Google Workspace or Microsoft Entra ID, you don’t need to rip and replace. You need a layer that makes those investments more secure and more education-appropriate — not a competing system.
What’s available for all schools in Spring and Summer 2026
Our roadmap addresses exactly what IT leaders say they need most: visibility, control, and trust.
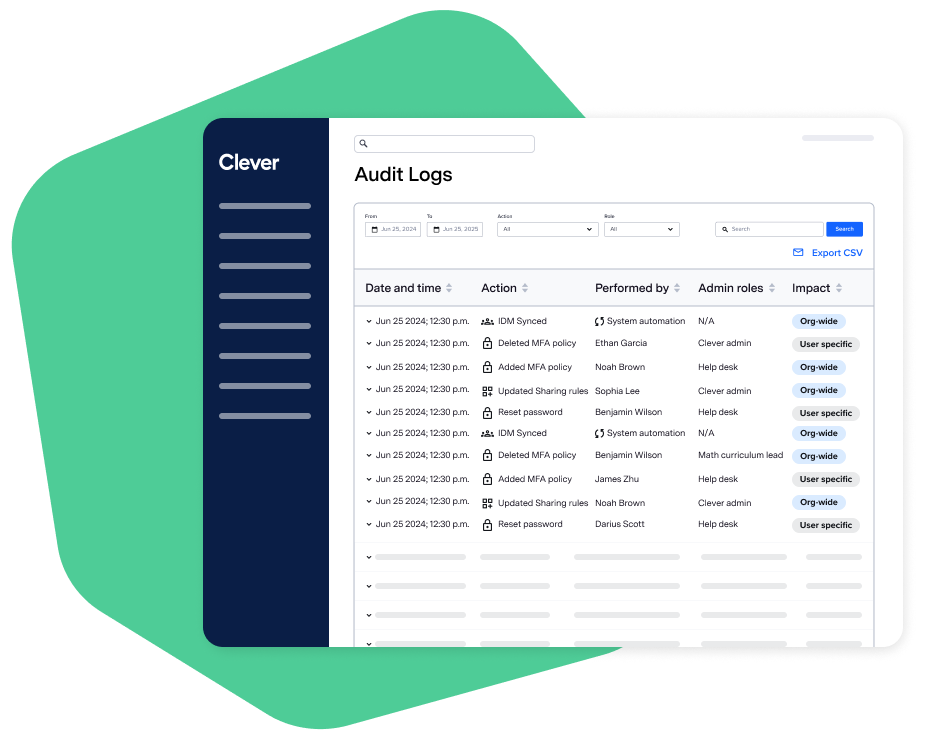
On visibility: a comprehensive audit log arriving by Back to School, downloadable MFA registration reports (a one-step answer for your cyber insurance provider), badge expiration tracking, direct Clever log export to SIEM solutions, and data changes in the dashboard after completing a sync conversion.
On control: granular MFA policies by group, multilingual student access (Spanish and British/Australian English to start), HR API integrations for staff data ingestion, and bulk password and MFA reset tools — so when an incident hits, you respond at scale, not one account at a time.
On trust: a new Microsoft Edge integration that establishes device trust for Classroom MFA — managed device gets a streamlined login, unmanaged device gets prompted automatically. Plus granular role-based access control, so admin access to one application doesn’t cascade across all of them.
Stop Adding Complexity. Start Bolting the Door.
36% of districts cite lack of dedicated cybersecurity staff as their top challenge. Budget pressure has risen from 23% in 2023 to 27% today. The forward in our 2026 report, written by Corey Lee, CTO for US Student Local Education at Microsoft, puts it plainly: education is among the most frequently targeted sectors, and attackers exploit the resource gap deliberately.
The path forward isn’t adding complexity — it’s building on the right foundation and making security simple enough that it actually gets deployed. Student MFA doesn’t require a phone. Automated provisioning doesn’t require a full-time IAM engineer. And most of Clever’s foundational security tools are available at no cost to school organizations.
Start with our Cybersecurity Blueprint — five steps aligned to global guidelines. Read the blueprint for your country
- United States: NIST guidelines and the K-12 Six Essential Cybersecurity Protections that you and your team can work through right now.
- United Kingdom: A framework aligned with UK Cyber Assessment Framework and Cyber Essentials, which will require MFA starting in April 2026.
- Australia: Aligned with Essential 8 and the NIST
→ Learn how to get started with Clever layered security solutions.

More to read

May 29, 2026
UK Primary School Switches to Clever for Secure, One-Click Access to AppsDiscover how Cornerstone C of E Primary School replaced risky shared logins with unique, secure credentials for every pupil, using Clever's single sign-on and Clever Badges to make classroom and home learning seamlessly accessible across all year groups.

May 29, 2026
18 Years of Manual Provisioning in Manitoba, Cleaned & Automated in MinutesPark West School Division's three-person IT team eliminated 18 years of manual account provisioning across 16 rural Manitoba schools — with Clever IDM making over 800 directory changes on day one and zero manual account requests ever since.

May 29, 2026
Calgary Academy: From Manual Passwords to Automated Identity in MinutesCalgary Academy eliminated week-long student account delays and closed a critical cybersecurity insurance gap by automating identity management and deploying MFA across all K–12 grades — including kindergarteners — with Clever IDM and Classroom MFA.